How to Recover Download Site Passwords from Mipony Downloader
In this article, you’ll learn where Mipony stores all your download site passwords, how they are protected, and how you can easily recover them.
Mipony Downloader Password Secrets
Mipony Downloader saves download site passwords in file called “mipony.xml” at following location
[Windows Vista/7/8/10] C:\Users\[user_name]\AppData\Roaming\Mipony\mipony.xml [Windows XP/2003] C:\Documents and Settings\[user_name]\Application Data\Mipony\mipony.xml
This XML file contains separate entries for storing login & password for each download site as shown below,
<property key="URapidgator" value="xenarmor" type="string" />
<property key="PRapidgator" value="pass123" type="string" />
Here first letter (U or P) in the “key” field indicates whether “value” is username or password.
How to Recover Mipony Downloader Passwords Automatically
Now you can easily & instantly recover all your lost passwords from Mipony Download Manager without any technical knowledge.
With just one click, XenArmor Downloader Password Recovery Pro can recover all your saved download site passwords from Mipony.
Follow these simple steps,
- Download & install the software from here
- Click on “Recover Passwords”
- Instantly see all your saved passwords from Mipony
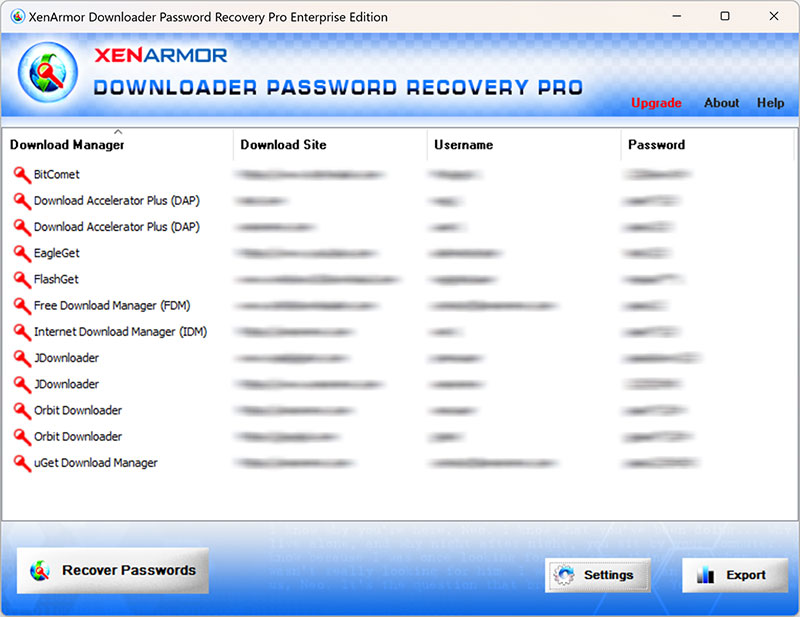
Here are the key features loved by users,
- Recover from 10+ Download Managers
- Recover from both 32-bit & 64-bit apps
- Extract from all profiles & custom locations
- Support command-line & automation
- Export passwords to PDF, HTML, CSV, JSON & more
👉 Free Download XenArmor Downloader Password Recovery Pro




